The challenge with signature based security and antivirus tools is you are vulnerable until the signature is released and distributed by the vendors. Palo Alto takes a different approach with it’s new Traps Endpoint Security that was recently released in the US.
While we won’t see it locally until later this year, blueAPACHE have been closely following its progress to quantify its effectiveness to help our emPOWER cloud-based clients better secure their endpoints.
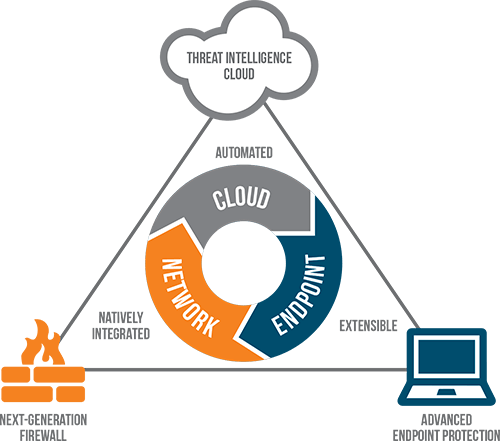
Traps is the third component of Palo Alto’s next-generation security platform. It is a very thin client that lives on the endpoint itself that consumes only 5Mb of memory and about a tenth of one percent on average of CPU utilisation.
Simply, it sits on the endpoint device and anytime a new process is opened Traps injects prevention modules into that process. So the second an attacker tries to utilise one of the known techniques they will run into one of the prevention modules and the attack is prevented.
There are currently only 24 techniques that attackers have at their disposal to try and exploit a system and Traps addresses all 24. These techniques rarely change – there have only been three new techniques in two years, and you guessed it; Traps already addresses these new methodologies as well.
The need for a new endpoint is growing. Scott Gainey, Palo Alto VP of Product Marketing, explains “If I’m outside of my corporate network operating on an unsecured Wi-Fi network my system is at risk. A simple drive-by-download of embedded malicious content in, say, an iframe could easily bypass existing anti-virus software, leaving nothing that could protect me from being infected. This is one of many examples that leave endpoints vulnerable.
“Another one is that we see a lot of highly targeted attacks that are utilising a threat that’s never been seen before and has been designed in such a way that it’s able to evade detection at the network security level. It could be based on a new zero-day vulnerability the attacker will use against a high-value target. Because this is based on an unknown vulnerability it’s missed by IPS/IDS. Our approach is effective at learning from these new attacks and routing new defenses back to the infrastructure so if that type of threat is used again it will be blocked. But if the attacker only uses it once then other areas of defense must kick in to protect an organisation.”
Traditional endpoint security companies that offer antivirus rely on signatures for defense, which requires prior knowledge in order to block the threat. These traditional vendors have large teams of people constantly defending threats once they are identified. The challenge with this approach is you are always a couple of steps behind the attacker community.
Gainey continues “There’s literally millions of forms of new malware that get generated each year. On a daily basis we see an average of over 20,000 new forms of malware. So companies with antivirus-based solutions have to build signatures against all of those new forms, then distribute those signatures out to all the endpoints. It’s an impossible situation to stay on top of.
“Similarly, technologies like discreet intrusion prevention or intrusion detection systems require prior knowledge to protect against vulnerabilities. So if it’s an unknown zero-day based vulnerability, IPS or IDS isn’t as effective. It can only block what it knows.”
Traps will be available in Asia Pacific during the second half of 2015. If you are interested in learning more, feel free to contact us directly and we will keep you informed.
Disclaimer: blueAPACHE is a Palo Alto Networks partner.
For more information:
To learn about your on-premise, cloud and endpoint security options, contact your blueAPACHE account manager.
To learn more about Palo Alto Traps, view their site.
To access the Palo Alto Traps datasheet, click here.